Introduction
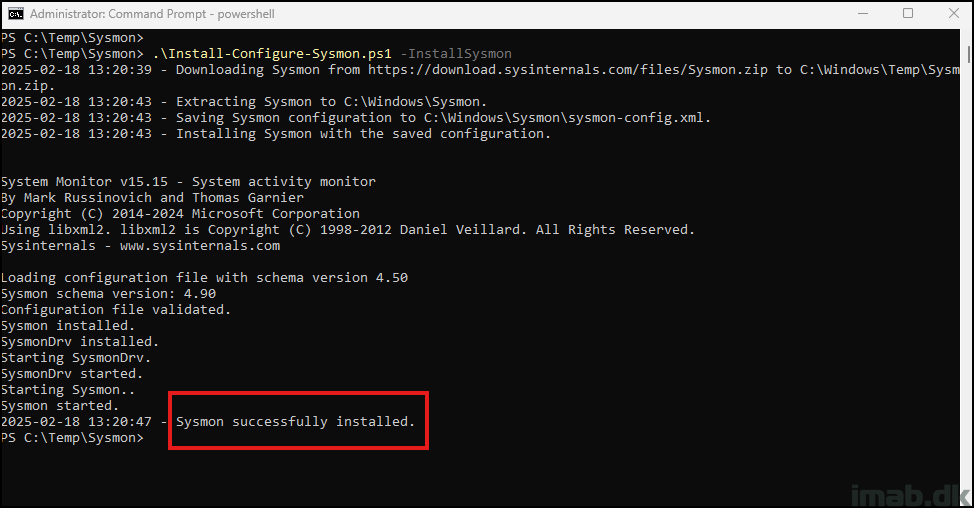
In today’s fast-paced digital world, quick response to security incidents is crucial. Sysmon (System Monitor) from Microsoft’s Sysinternals suite is an essential tool for detailed system monitoring and security analysis. However, traditional installation can be time-consuming, especially in urgent situations.
This blog post introduces a PowerShell script that automates the download, extraction, and installation of Sysmon, along with applying a pre-configured setup. This rapid deployment ensures your systems are monitored and protected within minutes, enhancing your incident response capabilities and maintaining a strong security posture.